
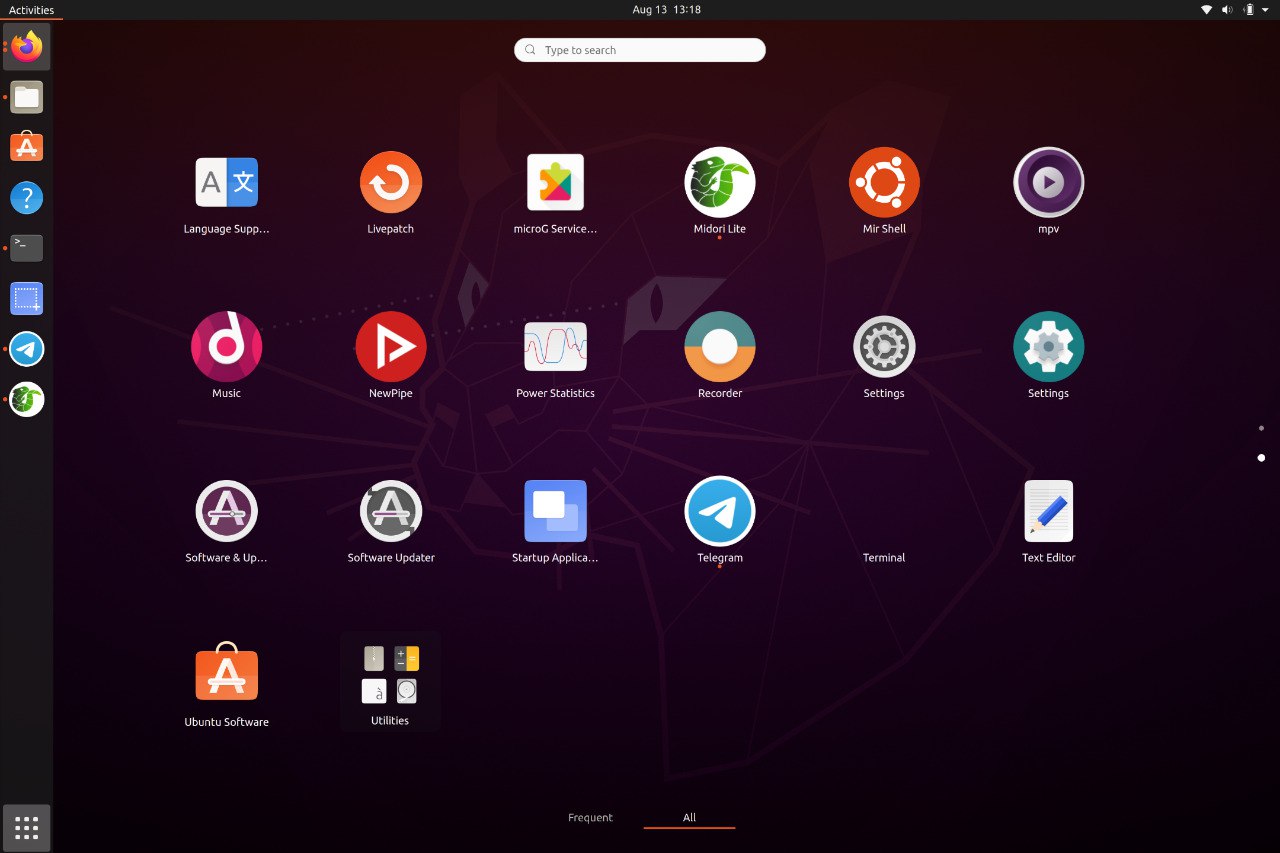
A container-based approach to boot a full Android system on regular GNU/Linux systems running Wayland based desktop environments.



A container-based approach to boot a full Android system on regular GNU/Linux systems running Wayland based desktop environments.


This editorial explains what boot9.bin contains in practical terms, why it became central to the 3DS hacking scene, the technical implications of having access to it, and the ethical and legal considerations anyone writing about or handling such files should weigh carefully.
The term boot9.bin refers to a low-level firmware image used by certain Nintendo 3DS-family devices. It occupies a highly privileged position in the device’s boot sequence: executed early during startup, it initializes hardware, sets up cryptographic keys and secure boot chains, and orchestrates handoff to higher-level firmware. Because of that privileged role, boot9.bin — when obtained in raw form — can reveal critical details about the console’s security architecture and, potentially, enable full control of the device.
Waydroid brings all the apps you love, right to your desktop, working side by side your Linux applications.
The Android inside the container has direct access to needed hardwares.
The Android runtime environment ships with a minimal customized Android system image based on LineageOS. The used image is currently based on Android 13
Our documentation site can be found at docs.waydro.id
Bug Reports can be filed on our repo Github Repo
Our development repositories are hosted on Github
Please refer to our installation docs for complete installation guide.
You can also manually download our images from
 SourceForge
SourceForge

For systemd distributions
Follow the install instructions for your linux distribution. You can find a list in our docs.
After installing you should start the waydroid-container service, if it was not started automatically:
sudo systemctl enable --now waydroid-container
Then launch Waydroid from the applications menu and follow the first-launch wizard.
If prompted, use the following links for System OTA and Vendor OTA:
https://ota.waydro.id/system
https://ota.waydro.id/vendor
For further instructions, please visit the docs site here
This editorial explains what boot9.bin contains in practical terms, why it became central to the 3DS hacking scene, the technical implications of having access to it, and the ethical and legal considerations anyone writing about or handling such files should weigh carefully.
The term boot9.bin refers to a low-level firmware image used by certain Nintendo 3DS-family devices. It occupies a highly privileged position in the device’s boot sequence: executed early during startup, it initializes hardware, sets up cryptographic keys and secure boot chains, and orchestrates handoff to higher-level firmware. Because of that privileged role, boot9.bin — when obtained in raw form — can reveal critical details about the console’s security architecture and, potentially, enable full control of the device.
Here are the members of our team







